More and more business is moving to the cloud and, given the concentration of providers and their interlinkages, it’s creating security challenges. In the US, 15 cloud providers account for 70% of the market.
The National Institute of Standards and Technology (NIST) describes the cloud as a model for enabling convenient, on-demand network access to a shared pool of configurable computing resources that can be rapidly provisioned and released with minimal management effort or service provider interaction.
A cloud solution is typically architected with multiple regions, where a region is a geographical location where users can run their resources, and is typically made up of multiple zones. All major cloud providers have multiple regions, located across the globe and within the US. For example, Rackspace has the fewest number of regions at 7 whereas Microsoft Azure has the most at 36.
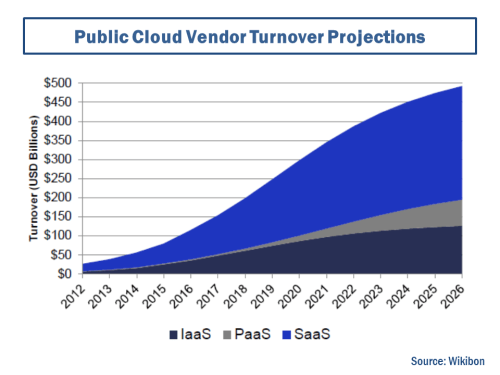
The industry is projected to grow at a compound annual growth rate of 36% between 2014 and 2026, as per the graph below. Software as a service (SaaS), platform as a service (PaaS), and infrastructure as a service (IaaS) are the types of cloud services sold.
Control of the underlying cloud infrastructure of networks, servers, operating systems, and storage is the responsibility of the cloud provider, with the user having control over the deployed applications and possibly configuration settings for the application-hosting environment.
Amazingly however, the main responsibility for protecting corporate data in the cloud lies not with the cloud provider but with the cloud customer, unless specifically agreed otherwise. Jay Heiser of Gartner commented that “we are in a cloud security transition period in which focus is shifting from the provider to the customer” and businesses “are learning that huge amounts of time spent trying to figure out if any particular cloud service provider is secure or not has virtually no payback”.
An organisation called the Cloud Security Alliance (CSA) issued its report on the security threats to the cloud. These include the usual threats such as data breaches, denial of service (DoS), advanced persistent threats (APTs) and malicious insiders. For the cloud, add in threats including insufficient access management, insecure user interfaces (UIs) and application programming interfaces (APIs), and shared technology vulnerabilities.
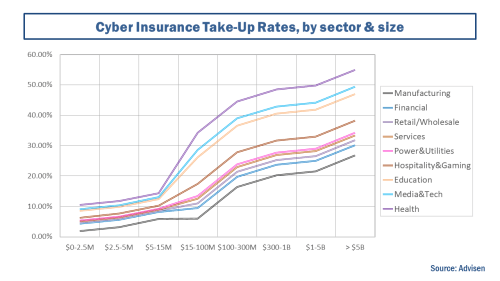
Cyber security is an important issue today and many businesses, particularly larger business are turning to insurance to mitigate the risks to their organisations, as the graph below on cyber insurance take-up rates shows.
Lloyds of London recently released an interesting report called Cloud Down that estimated the e-business interruption costs in the US arising from the sustained loss of access to a cloud service provider. The report estimates, using a standard catastrophic modelling framework from AIR, a cyber incident that takes a top 3 cloud provider offline in the US for 3-6 days would result in ground-up loss central estimates between $7-15 billion and insured losses between $1.5-3 billion. By necessity, the assumptions used in the analysis are fairly crude and basic.
Given the number of bad actors in the cyber world, particularly those who may intend to cause maximum disruption, security failings around the cloud could, in my view, result in losses of many multiples of those projected by Lloyds if several cloud providers are taken down for longer periods. And that’s scary.